Main Page: Difference between revisions
Juho Kunsola (talk | contribs) m (mv pic) |
Juho Kunsola (talk | contribs) (+ no pornography + clarifying that the main problem is with synthetic porn + fixing links) |
||
| Line 34: | Line 34: | ||
{{#lst:Synthetic human-like fakes|definitions-of-synthetic-human-like-fakes}} | {{#lst:Synthetic human-like fakes|definitions-of-synthetic-human-like-fakes}} | ||
Welcome to Stop Synthetic Filth! wiki - [[SSF:About|A wiki]] with <font color="red>no pornography</font>, but instead {{NUMBEROFARTICLES}} articles with {{NUMBEROFEDITS}} edits about discovering ways of stopping and minimizing the damage from '''naked [[synthetic human-like fakes]]''' [[#Synthetic human-like fakes (transcluded)|(transcluded below)]] i.e '''[[Synthetic human-like fakes#Digital look-alikes|digital look-alikes]] and [[Synthetic human-like fakes#Digital sound-alikes|digital sound-alikes]]''' that result from '''covert modeling''' i.e. [[Glossary#Appearance and voice theft|thieving]] of the '''human appearance''' and of the '''naked human voice'''. | |||
'''[[Biblical explanation - The books of Daniel and Revelation]]''', wherein [[Biblical explanation - The books of Daniel and Revelation#Daniel 7|Daniel 7]] and [[Biblical explanation - The books of Daniel and Revelation#Revelation 13|Revelation 13]] we are warned of this age of industrial filth, is for those who believe in Jesus. | '''[[Biblical explanation - The books of Daniel and Revelation]]''', wherein [[Biblical explanation - The books of Daniel and Revelation#Daniel 7|Daniel 7]] and [[Biblical explanation - The books of Daniel and Revelation#Revelation 13|Revelation 13]] we are warned of this age of industrial filth, is for those who believe in Jesus. | ||
| Line 51: | Line 51: | ||
* [[File:Flag of Sweden.svg|link=https://stop-synthetic-filth.org/wp/sv/hemsida/|25px]] [https://stop-synthetic-filth.org/wp/sv/hemsida/ '''Stoppa syntetisk orenhet!''' hemsida på svenska '''SSO!'''] | * [[File:Flag of Sweden.svg|link=https://stop-synthetic-filth.org/wp/sv/hemsida/|25px]] [https://stop-synthetic-filth.org/wp/sv/hemsida/ '''Stoppa syntetisk orenhet!''' hemsida på svenska '''SSO!'''] | ||
* [[File:Flag_of_Estonia.png|link=https://stop-synthetic-filth.org/wp/et/koduleht/|25px]] [https://stop-synthetic-filth.org/wp/et/koduleht/ '''Stopp sünteetisele saastale!''' koduleht eesti keeles '''SSS!'''] | * [[File:Flag_of_Estonia.png|link=https://stop-synthetic-filth.org/wp/et/koduleht/|25px]] [https://stop-synthetic-filth.org/wp/et/koduleht/ '''Stopp sünteetisele saastale!''' koduleht eesti keeles '''SSS!'''] | ||
</big> | |||
<nowiki>#</nowiki>SSF!'s predecessor domain is [https://ban-covert-modeling.org/ Ban-Covert-Modeling.org #BCM!] [[File:BCM-logo-favicon-ico-C!.png|link=https://ban-covert-modeling.org/|36px]] | <nowiki>#</nowiki>SSF!'s predecessor domain is [https://ban-covert-modeling.org/ Ban-Covert-Modeling.org #BCM!] [[File:BCM-logo-favicon-ico-C!.png|link=https://ban-covert-modeling.org/|36px]] | ||
[[SSF:About|SSF! wiki]] is an open non-profit public service by [[User:Juho Kunsola|Juho Kunsola]] [https://byjuho.fi (my official website)] | [[SSF:About|SSF! wiki]] is an open non-profit public service by [[User:Juho Kunsola|Juho Kunsola]] [https://byjuho.fi (my official website)] | ||
[[File:Stop-synthetic-filth.org-is-hosted-green.png|thumb|center|[[SSF:About|Stop Synthetic Filth! wiki]] is hosted in Finland [https://byjuho.fi by Juho Kunsola] at a hosting business that uses electricity from renewable sources only. ([https://www.thegreenwebfoundation.org/green-web-check/?url= | [[File:Stop-synthetic-filth.org-is-hosted-green.png|thumb|center|link=https://www.thegreenwebfoundation.org/green-web-check/?url=stop-synthetic-filth.org|[[SSF:About|Stop Synthetic Filth! wiki]] is hosted in Finland [https://byjuho.fi by Juho Kunsola] at a hosting business that uses electricity from renewable sources only. ([https://www.thegreenwebfoundation.org/green-web-check/?url=stop-synthetic-filth.org Check])]] | ||
---- | ---- | ||
= Introduction to synthetic filth = | = Introduction to synthetic filth = | ||
Revision as of 20:12, 8 December 2020
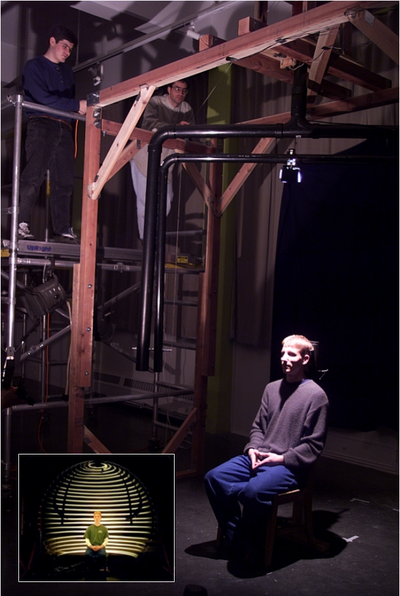
It consists of two w:rotary axes with w:height and w:radius control. A w:light source and a w:polarizer in front of the light source were placed on one arm and a camera and the other polarizer on the other arm. See picture below, for what they did to the captured reflection.
Original image by Debevec et al. – Copyright ACM 2000 – https://dl.acm.org/citation.cfm?doid=311779.344855 – Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page.
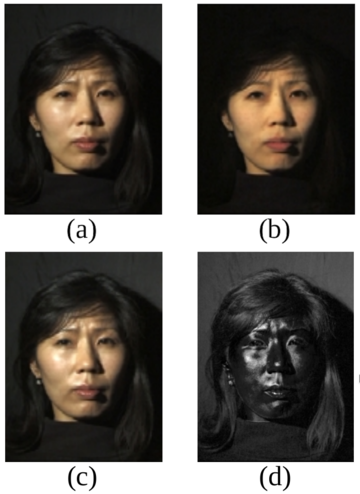
(a) Normal image in dot lighting
(b) Image of the diffuse reflection which is caught by placing a vertical polarizer in front of the light source and a horizontal in the front the camera
(c) Image of the highlight specular reflection which is caught by placing both polarizers vertically
(d) Subtraction of c from b, which yields the specular component
Images are scaled to seem to be the same luminosity.
Original image by Debevec et al. – Copyright ACM 2000 – https://dl.acm.org/citation.cfm?doid=311779.344855 – Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page.

Man of Steel produced by DC Entertainment and Legendary Pictures, distributed by Warner Bros. Pictures. Modification done by Reddit user "derpfakes".
This is a sample from a copyrighted video recording. The person who uploaded this work and first used it in an article, and subsequent people who use it in articles, assert that this qualifies as fair use.
When the camera does not exist, but the subject being imaged with a simulation of a (movie) camera deceives the watcher to believe it is some living or dead person it is a digital look-alike.
In 2017-2018 this started to be referred to as w:deepfake, even though altering video footage of humans with a computer with a deceiving effect is actually 20 yrs older than the name "deep fakes" or "deepfakes".[1][2]
When it cannot be determined by human testing or media forensics whether some fake voice is a synthetic fake of some person's voice, or is it an actual recording made of that person's actual real voice, it is a pre-recorded digital sound-alike. This is now commonly referred to as w:audio deepfake.
Real-time digital look-and-sound-alike in a video call was used to defraud a substantial amount of money in 2023.[3]
Welcome to Stop Synthetic Filth! wiki - A wiki with no pornography, but instead 23 articles with 4,557 edits about discovering ways of stopping and minimizing the damage from naked synthetic human-like fakes (transcluded below) i.e digital look-alikes and digital sound-alikes that result from covert modeling i.e. thieving of the human appearance and of the naked human voice.
Biblical explanation - The books of Daniel and Revelation, wherein Daniel 7 and Revelation 13 we are warned of this age of industrial filth, is for those who believe in Jesus.
Adequate Porn Watcher AI (transcluded below) is a concept for an AI to protect the humans against synthetic filth attacks by looking for porn that should not be.
How to protect yourself and others from covert modeling (transcluded below)
Law proposals | Current laws and their application | Atheist explanation | Mediatheque | Glossary | Resources | About this wiki | Scratchpad for quick drafting
Synopses of SSF! wiki in other languages
 Stop Synthetic Filth! wordpress in English SSF!
Stop Synthetic Filth! wordpress in English SSF! Arrêtons les saletés synthétiques! accueil en français ASS!
Arrêtons les saletés synthétiques! accueil en français ASS! Stoppi synteettiselle saastalle! kotisivu suomeksi SSS!
Stoppi synteettiselle saastalle! kotisivu suomeksi SSS! Stoppa syntetisk orenhet! hemsida på svenska SSO!
Stoppa syntetisk orenhet! hemsida på svenska SSO! Stopp sünteetisele saastale! koduleht eesti keeles SSS!
Stopp sünteetisele saastale! koduleht eesti keeles SSS!
#SSF!'s predecessor domain is Ban-Covert-Modeling.org #BCM! ![]()
SSF! wiki is an open non-profit public service by Juho Kunsola (my official website)

Introduction to synthetic filth
Since the early 00's it has become (nearly) impossible to determine in still or moving pictures what is an image of a human, imaged with a (movie) camera and what on the other hand is a simulation of an image of a human imaged with a simulation of a camera. When there is no camera and the target being imaged with a simulation looks deceptively like some real human, dead or living, it is a digital look-alike.
Now in the late 2010's the equivalent thing is happening to our voices i.e. they can be stolen to some extent with the 2016 prototypes like w:Adobe Inc.'s w:Adobe Voco and w:Google's w:DeepMind w:WaveNet and made to say anything. When it is not possible to determine with human testing or testing with technological means what is a recording of some living or dead person's real voice and what is a simulation it is a digital sound-alike. 2018 saw the publication of Google Research's sound-like-anyone machine (transcluded below) at the w:NeurIPS conference and by the end of 2019 Symantec research had learned of 3 cases where digital sound-alike technology had been used for crimes.[4]
Therefore it is high time to act and to criminalize covert modeling of the naked human voice and synthesis from a covert voice model!
Covert modeling poses growing threats to
- The right to be the only one that looks like me (compromised by digital look-alikes)
- The right to be the only one able to make recordings that sound like me (compromised by digital sound-alikes)
And these developments have various severe effects on the right to privacy, provability by audio and video evidence and deniability.
Synthetic human-like fakes (transcluded)
Transcluded from Synthetic human-like fakes
Definitions
When the camera does not exist, but the subject being imaged with a simulation of a (movie) camera deceives the watcher to believe it is some living or dead person it is a digital look-alike.
In 2017-2018 this started to be referred to as w:deepfake, even though altering video footage of humans with a computer with a deceiving effect is actually 20 yrs older than the name "deep fakes" or "deepfakes".[1][2]
When it cannot be determined by human testing or media forensics whether some fake voice is a synthetic fake of some person's voice, or is it an actual recording made of that person's actual real voice, it is a pre-recorded digital sound-alike. This is now commonly referred to as w:audio deepfake.
Real-time digital look-and-sound-alike in a video call was used to defraud a substantial amount of money in 2023.[3]
- Read more about synthetic human-like fakes, see and support organizations and events against synthetic human-like fakes and what they are doing, what kinds of Laws against synthesis and other related crimes have been formulated, examine the SSFWIKI timeline of synthetic human-like fakes or view the Mediatheque.

Click on the picture or Obama's appearance thieved - a public service announcement digital look-alike by Monkeypaw Productions and Buzzfeed to view an April 2018 public service announcement moving digital look-alike made to appear Obama-like. The video is accompanied with imitator sound-alike, and was made by w:Monkeypaw Productions (.com) in conjunction with w:BuzzFeed (.com). You can also View the same video at YouTube.com.[5]
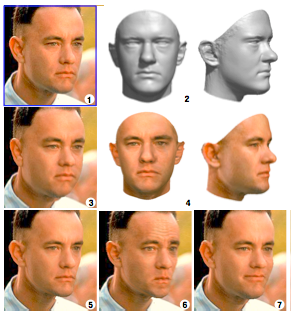
(1) Sculpting a morphable model to one single picture
(2) Produces 3D approximation
(4) Texture capture
(3) The 3D model is rendered back to the image with weight gain
(5) With weight loss
(6) Looking annoyed
(7) Forced to smile Image 2 by Blanz and Vettel – Copyright ACM 1999 – http://dl.acm.org/citation.cfm?doid=311535.311556 – Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page.
Digital look-alikes
Introduction to digital look-alikes
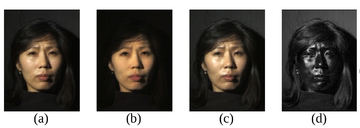
(a) Normal image in dot lighting
(b) Image of the diffuse reflection which is caught by placing a vertical polarizer in front of the light source and a horizontal in the front the camera
(c) Image of the highlight specular reflection which is caught by placing both polarizers vertically
(d) Subtraction of c from b, which yields the specular component
Images are scaled to seem to be the same luminosity.
Original image by Debevec et al. – Copyright ACM 2000 – https://dl.acm.org/citation.cfm?doid=311779.344855 – Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page.

Original picture by w:Paul Debevec et al. - Copyright ACM 2000 https://dl.acm.org/citation.cfm?doid=311779.344855
In the cinemas we have seen digital look-alikes for over 20 years. These digital look-alikes have "clothing" (a simulation of clothing is not clothing) or "superhero costumes" and "superbaddie costumes", and they don't need to care about the laws of physics, let alone laws of physiology. It is generally accepted that digital look-alikes made their public debut in the sequels of The Matrix i.e. w:The Matrix Reloaded and w:The Matrix Revolutions released in 2003. It can be considered almost certain, that it was not possible to make these before the year 1999, as the final piece of the puzzle to make a (still) digital look-alike that passes human testing, the reflectance capture over the human face, was made for the first time in 1999 at the w:University of Southern California and was presented to the crème de la crème of the computer graphics field in their annual gathering SIGGRAPH 2000.[6]
“Do you think that was w:Hugo Weaving's left cheekbone that w:Keanu Reeves punched in with his right fist?”
The problems with digital look-alikes
Extremely unfortunately for the humankind, organized criminal leagues, that posses the weapons capability of making believable looking synthetic pornography, are producing on industrial production pipelines terroristic synthetic pornography[footnote 1] by animating digital look-alikes and distributing it in the murky Internet in exchange for money stacks that are getting thinner and thinner as time goes by.
These industrially produced pornographic delusions are causing great human suffering, especially in their direct victims, but they are also tearing our communities and societies apart, sowing blind rage, perceptions of deepening chaos, feelings of powerlessness and provoke violence.
These kinds of hate illustration increases and strengthens hate feeling, hate thinking, hate speech and hate crimes and tears our fragile social constructions apart and with time perverts humankind's view of humankind into an almost unrecognizable shape, unless we interfere with resolve.
Children-like sexual abuse images
Sadly by 2023 there is a market for synthetic human-like sexual abuse material that looks like children. See 'Illegal trade in AI child sex abuse images exposed' at bbc.com 2023-06-28 reports w:Stable Diffusion being abused to produce this kind of images. The w:Internet Watch Foundation also reports on the alarming existence of production of synthetic human-like sex abuse material portraying minors. See 'Prime Minister must act on threat of AI as IWF ‘sounds alarm’ on first confirmed AI-generated images of child sexual abuse' at iwf.org.uk (2023-08-18)
Fixing the problems from digital look-alikes
We need to move on 3 fields: legal, technological and cultural.
Technological: Computer vision system like FacePinPoint.com for seeking unauthorized pornography / nudes used to exist 2017-2021 and could be revived if funding is found. It was a service practically identical with SSFWIKI original concept Adequate Porn Watcher AI (concept).
Legal: Legislators around the planet have been waking up to this reality that not everything that seems a video of people is a video of people and various laws have been passed to protect humans and humanity from the menaces of synthetic human-like fakes, mostly digital look-alikes so far, but hopefully humans will be protected also fro other aspects of synthetic human-like fakes by laws. See Laws against synthesis and other related crimes
Age analysis and rejuvenating and aging syntheses
- 'An Overview of Two Age Synthesis and Estimation Techniques' at arxiv.org (.pdf), submitted for review on 2020-01-26
- 'Dual Reference Age Synthesis' at sciencedirect.com (preprint at arxiv.org) published on 2020-10-21 in w:Neurocomputing (journal)
- 'A simple automatic facial aging/rejuvenating synthesis method' at ieeexplore.ieee.org read free at researchgate.net, published at the proceedings of the 2011 IEEE International Conference on Systems, Man and Cybernetics
- 'Age Synthesis and Estimation via Faces: A Survey' at ieeexplore.ieee.org (paywall) at researchgate.net published November 2010
Temporal limit of digital look-alikes

w:History of film technology has information about where the border is.
Digital look-alikes cannot be used to attack people who existed before the technological invention of film. For moving pictures the breakthrough is attributed to w:Auguste and Louis Lumière's w:Cinematograph premiered in Paris on 28 December 1895, though this was only the commercial and popular breakthrough, as even earlier moving pictures exist. (adapted from w:History of film)
The w:Kinetoscope is an even earlier motion picture exhibition device. A prototype for the Kinetoscope was shown to a convention of the National Federation of Women's Clubs on May 20, 1891.[7] The first public demonstration of the Kinetoscope was held at the Brooklyn Institute of Arts and Sciences on May 9, 1893. (Wikipedia)[7]
Digital sound-alikes
University of Florida published an antidote to synthetic human-like fake voices in 2022
2022 saw a brilliant counter-measure presented to peers at the 31st w:USENIX Security Symposium 10-12 August 2022 by w:University of Florida Detecting deep-fake audio through vocal tract reconstruction.
The university's foundation has applied for a patent and let us hope that they will w:copyleft the patent as this protective method needs to be rolled out to protect the humanity.
Below transcluded from the article
Detecting deep-fake audio through vocal tract reconstruction is an epic scientific work, against fake human-like voices, from the w:University of Florida in published to peers in August 2022.


The work Who Are You (I Really Wanna Know)? Detecting Audio DeepFakes Through Vocal Tract Reconstruction at usenix.org, presentation page, version included in the proceedings[8] and slides from researchers of the Florida Institute for Cybersecurity Research (FICS) at fics.institute.ufl.edu in the w:University of Florida received funding from the w:Office of Naval Research and was presented on 2022-08-11 at the 31st w:USENIX Security Symposium.
This work was done by PhD student Logan Blue, Kevin Warren, Hadi Abdullah, Cassidy Gibson, Luis Vargas, Jessica O’Dell, Kevin Butler and Professor Patrick Traynor.
The University of Florida Research Foundation Inc has filed for and received an US patent titled 'Detecting deep-fake audio through vocal tract reconstruction' registration number US20220036904A1 (link to patents.google.com) with 20 claims. The patent application was published on Thursday 2022-02-03. The patent application was approved on 2023-07-04 and has an adjusted expiration date of Sunday 2041-12-29. PhD student Logan Blue and professor Patrick Traynor wrote an article for the general public on the work titled Deepfake audio has a tell – researchers use fluid dynamics to spot artificial imposter voices at theconversation.com[9] that was published Tuesday 2022-09-20 and permanently w:copylefted it under Creative Commons Attribution-NoDerivatives (CC-BY-ND).
This new counter-measure needs to be rolled out to humans to protect humans against the fake human-like voices.
Below is an exact copy of the original article from the SSF! wordpress titled "Amazing method and results from University of Florida scientists in 2022 against the menaces of digital sound-alikes / audio deepfakes". Thank you to the original writers for having the wisdom of licensing the article under CC-BY-ND.
On known history of digital sound-alikes
The first English speaking digital sound-alikes were first introduced in 2016 by Adobe and Deepmind, but neither of them were made publicly available.
Then in 2018 at the w:Conference on Neural Information Processing Systems (NeurIPS) the work 'Transfer Learning from Speaker Verification to Multispeaker Text-To-Speech Synthesis' (at arXiv.org) was presented. The pre-trained model is able to steal voices from a sample of only 5 seconds with almost convincing results
The Iframe below is transcluded from 'Audio samples from "Transfer Learning from Speaker Verification to Multispeaker Text-To-Speech Synthesis"' at google.gituhub.io, the audio samples of a sound-like-anyone machine presented as at the 2018 w:NeurIPS conference by Google researchers.
Have a listen.
Observe how good the "VCTK p240" system is at deceiving to think that it is a person that is doing the talking.
Reporting on the sound-like-anyone-machines
- "Artificial Intelligence Can Now Copy Your Voice: What Does That Mean For Humans?" May 2019 reporting at forbes.com on w:Baidu Research'es attempt at the sound-like-anyone-machine demonstrated at the 2018 w:NeurIPS conference.
The to the right video 'This AI Clones Your Voice After Listening for 5 Seconds' by '2 minute papers' at YouTube describes the voice thieving machine presented by Google Research in w:NeurIPS 2018.
Documented crimes with digital sound-alikes
In 2019 reports of crimes being committed with digital sound-alikes started surfacing. As of Jan 2022 no reports of other types of attack than fraud have been found.
2019 digital sound-alike enabled fraud
By 2019 digital sound-alike anyone technology found its way to the hands of criminals. In 2019 Symantec researchers knew of 3 cases where digital sound-alike technology had been used for w:crime.[10]
Of these crimes the most publicized was a fraud case in March 2019 where 220,000€ were defrauded with the use of a real-time digital sound-alike.[11] The company that was the victim of this fraud had bought some kind of cyberscam insurance from French insurer w:Euler Hermes and the case came to light when Mr. Rüdiger Kirsch of Euler Hermes informed w:The Wall Street Journal about it.[12]
Reporting on the 2019 digital sound-alike enabled fraud
- Fraudsters Used AI to Mimic CEO’s Voice in Unusual Cybercrime Case at wsj.com original reporting, date unknown, updated 2019-08-30[11]
- "Fake voices 'help cyber-crooks steal cash'" at bbc.com July 2019 reporting [13]
- "An artificial-intelligence first: Voice-mimicking software reportedly used in a major theft" at washingtonpost.com documents a w:fraud committed with digital sound-like-anyone-machine, July 2019 reporting.[10]
- A Voice Deepfake Was Used To Scam A CEO Out Of $243,000 at forbes.com, 2019-09-03 reporting[12]
2020 digital sound-alike fraud attempt
In June 2020 fraud was attempted with a poor quality pre-recorded digital sound-alike with delivery method was voicemail. (Listen to a redacted clip at soundcloud.com) The recipient in a tech company didn't believe the voicemail to be real and alerted the company and they realized that someone tried to scam them. The company called in Nisos to investigate the issue. Nisos analyzed the evidence and they were certain it was a fake, but had aspects of a cut-and-paste job to it. Nisos prepared a report titled "The Rise of Synthetic Audio Deepfakes" at nisos.com on the issue and shared it with Motherboard, part of w:Vice (magazine) prior to its release.[14]
2021 digital sound-alike enabled fraud
The 2nd publicly known fraud done with a digital sound-alike[1st seen in 1] took place on Friday 2021-01-15. A bank in Hong Kong was manipulated to wire money to numerous bank accounts by using a voice stolen from one of the their client company's directors. They managed to defraud $35 million of the U.A.E. based company's money.[15]. This case came into light when Forbes saw a document where the U.A.E. financial authorities were seeking administrative assistance from the US authorities towards recovering a small portion of the defrauded money that had been sent to bank accounts in the USA.[15]
Reporting on the 2021 digital sound-alike enabled fraud
- Fraudsters Cloned Company Director’s Voice In $35 Million Bank Heist, Police Find at forbes.com 2021-10-14 original reporting
- Deepfaked Voice Enabled $35 Million Bank Heist in 2020 at unite.ai[1st seen in 1] reporting updated on 2021-10-15
- USD 35m voice cloning heist at aiaaic.org, October 2021 AIAAIC repository entry
More fraud cases with digital sound-alikes
- They thought loved ones were calling for help. It was an AI scam. at washingtonpost.com, March 2023 reporting
Example of a hypothetical 4-victim digital sound-alike attack
A very simple example of a digital sound-alike attack is as follows:
Someone puts a digital sound-alike to call somebody's voicemail from an unknown number and to speak for example illegal threats. In this example there are at least two victims:
- Victim #1 - The person whose voice has been stolen into a covert model and a digital sound-alike made from it to frame them for crimes
- Victim #2 - The person to whom the illegal threat is presented in a recorded form by a digital sound-alike that deceptively sounds like victim #1
- Victim #3 - It could also be viewed that victim #3 is our law enforcement systems as they are put to chase after and interrogate the innocent victim #1
- Victim #4 - Our judiciary which prosecutes and possibly convicts the innocent victim #1.
Examples of speech synthesis software not quite able to fool a human yet
Some other contenders to create digital sound-alikes are though, as of 2019, their speech synthesis in most use scenarios does not yet fool a human because the results contain tell tale signs that give it away as a speech synthesizer.
- Lyrebird.ai (listen)
- CandyVoice.com (test with your choice of text)
- Merlin, a w:neural network based speech synthesis system by the Centre for Speech Technology Research at the w:University of Edinburgh
- 'Neural Voice Cloning with a Few Samples at papers.nips.cc, w:Baidu Research'es shot at sound-like-anyone-machine did not convince in 2018
Temporal limit of digital sound-alikes

The temporal limit of whom, dead or living, the digital sound-alikes can attack is defined by the w:history of sound recording.
The article starts by mentioning that the invention of the w:phonograph by w:Thomas Edison in 1877 is considered the start of sound recording.
The phonautograph is the earliest known device for recording w:sound. Previously, tracings had been obtained of the sound-producing vibratory motions of w:tuning forks and other objects by physical contact with them, but not of actual sound waves as they propagated through air or other media. Invented by Frenchman W:Édouard-Léon Scott de Martinville, it was patented on March 25, 1857.[16]
Apparently, it did not occur to anyone before the 1870s that the recordings, called phonautograms, contained enough information about the sound that they could, in theory, be used to recreate it. Because the phonautogram tracing was an insubstantial two-dimensional line, direct physical playback was impossible in any case. Several phonautograms recorded before 1861 were successfully played as sound in 2008 by optically scanning them and using a computer to process the scans into digital audio files. (Wikipedia)

What should we do about digital sound-alikes?
Living people can defend[footnote 2] themselves against digital sound-alike by denying the things the digital sound-alike says if they are presented to the target, but dead people cannot. Digital sound-alikes offer criminals new disinformation attack vectors and wreak havoc on provability.
For these reasons the bannable raw materials i.e. covert voice models should be prohibited by law in order to protect humans from abuse by criminal parties.
It is high time to act and to criminalize the covert modeling of human voice!
Text syntheses
w:Chatbots and w:spamming have existed for a longer time, but only now armed with AI they are becoming more deceiving.
In w:natural language processing development in w:natural-language understanding leads to more cunning w:natural-language generation AI.
w:Large language models (LLM) are very large w:language models consisting of a w:neural network with many parameters.
w:OpenAI's w:Generative Pre-trained Transformer (GPT) is a left-to-right w:transformer (machine learning model)-based text generation model succeeded by w:GPT-2 and w:GPT-3
November 2022 saw the publication of OpenAI's w:ChatGPT, a conversational artificial intelligence.
w:Bard (chatbot) is a conversational w:generative artificial intelligence w:chatbot developed by w:Google, based on the w:LaMDA family of w:large language models. It was developed as a direct response to the rise of w:OpenAI's w:ChatGPT, and was released in March 2023. (Wikipedia)
Reporting / announcements (in reverse chronology)
- Reinventing search with a new AI-powered Microsoft Bing and Edge, your copilot for the web at blogs.microsoft.com February 2023 (2023-02-07). The new improved Bing, available only in Microsoft's Edge browser is reportedly based on a language model refined from GPT 3.5.[17]
- New AI classifier for indicating AI-written text at openai.com, a January 2023 blog post about OpenAI's AI classifier for detecting AI-written texts.
- Introducing ChatGPT at openai.com November 2022 (2022-11-30)
- 'A college kid’s fake, AI-generated blog fooled tens of thousands. This is how he made it.' at technologyreview.com August 2020 reporting in the w:MIT Technology Review by Karen Hao about GPT-3.
- 'OpenAI’s latest AI text generator GPT-3 amazes early adopters' at siliconangle.com July 2020 reporting on GPT-3
- OpenAI releases the full version of GPT-2 at openai.com in August 2019
- 'OpenAI releases curtailed version of GPT-2 language model' at venturebeat.com, August 2019 reporting on the original release of of the curtailed version of GPT-2
External links
- "Detection of Fake and False News (Text Analysis): Approaches and CNN as Deep Learning Model" at analyticsteps.com, a 2019 summmary written by Shubham Panth.
Detectors for synthesized texts
Introduction of w:ChatGPT by OpenAI brought the need for software to detect machine-generated texts.
Try AI plagiarism detection for free
- AI Content Detector at contentdetector.ai- AI Content Detector - Detect ChatGPT Plagiarism (try for free)
- AI Text Classifier at platform.openai.com- The AI Text Classifier is a fine-tuned GPT model that predicts how likely it is that a piece of text was generated by AI from a variety of sources, such as ChatGPT. (free account required)
- GPT Radar at gptradar.com - AI text detector app (try for free)[1st seen in 2]
- GPTZero at gptzero.me - The World's #1 AI Detector with over 1 Million Users (try for free)
- Plagiarism Checker at copyleaks.com- Plagiarism Checker by Copyleaks (try for free)[1st seen in 2]
- https://gowinston.ai/ - The most powerful AI content detection solution (free-tier available)[1st seen in 2]
- ZeroGPT at zerogpt.com[1st seen in 2] - GPT-4 And ChatGPT detector by ZeroGPT: detect OpenAI text - ZeroGPT the most Advanced and Reliable Chat GPT and GPT-4 detector tool (try for free)
For-a-fee AI plagiarism detection tools
- https://originality.ai/ - The Most Accurate AI Content Detector and Plagiarism Checker Built for Serious Content Publishers[1st seen in 2]
- https://www.turnitin.com/ - Empower students to do their best, original work[1st seen in 2]
Handwriting syntheses
Handwriting syntheses could be used
- Defensively, to hide one's handwriting style from public view
- Offensively, to thieve somebody else's handwriting style
If the handwriting-like synthesis passes human and media forensics testing, it is a digital handwrite-alike.
Here we find a possible risk similar to that which became a reality, when the w:speaker recognition systems turned out to be instrumental in the development of digital sound-alikes. After the knowledge needed to recognize a speaker was w:transferred into a generative task in 2018 by Google researchers, we no longer cannot effectively determine for English speakers which recording is human in origin and which is from a machine origin.
Handwriting-like syntheses: w:Recurrent neural networks (RNN) seem are a popular choice for this task.
- GitHub topic handwriting-synthesis has 29 public repositories as of September 2021.
- GitHub topic handwriting-generation has 21 public repositories as of September 2021.
- Deep imitator: Handwriting calligraphy imitation via deep attention networks' at sciencedirect.com, published in w:Pattern Recognition (journal) in August 2020.
- Scribe - Generating Realistic Handwriting with TensorFlow at greydanus.github.io blog post published on 2016-08-21. Scribe code at github.com
- My Text in Your Handwriting at dl.acm.org, a system from w:University College London published on 2016-05-18 in w:ACM Transactions on Graphics.[1st seen in 3]
- Generating Sequences With Recurrent Neural Networks at arxiv.org by Alex Graves published on 2013-08-04 in Neural and Evolutionary Computing.
- Recurrent neural network handwriting generation demo at cs.toronto.edu is a demonstration site for publication
- Calligrapher.ai - Realistic computer-generated handwriting - The user may control parameters: speed, legibility, stroke width and style. The domain is registered by some organization in Iceland and the website offers no about-page[1st seen in 4]. According to this reddit post Calligrapher.ai is based on Graves' 2013 work, but "adds an w:inference model to allow for sampling latent style vectors (similar to the VAE model used by SketchRNN)".[18]
Handwriting recognition
- w:Handwriting recognition (HWR), also known as Handwritten Text Recognition (HTR), is the ability of a computer to receive and interpret intelligible w:handwritten input (Wikipedia)
- w:Intelligent word recognition, or IWR, is the recognition of unconstrained handwritten words.[19] (Wikipedia)
- GitHub topic handwriting-recognition contains 238 repositories as of September 2021.
Singing syntheses
As of 2020 the digital sing-alikes may not yet be here, but when we hear a faked singing voice and we cannot hear that it is fake, then we will know. An ability to sing does not seem to add much hostile capabilities compared to the ability to thieve spoken word.
- 'Fast and High-Quality Singing Voice Synthesis System based on Convolutional Neural Networks' at arxiv.org, a 2019 singing voice synthesis technique using w:convolutional neural networks (CNN). Accepted into the 2020 International Conference on Acoustics, Speech, and Signal Processing (ICASSP).
- 'State of art of real-time singing voice synthesis' at compmus.ime.usp.br presented at the 2019 17th Brazilian Symposium on Computer Music
- 'Synthesis and expressive transformation of singing voice' at theses.fr as .pdf a 2017 doctorate thesis by Luc Ardaillon
- 'Synthesis of the Singing Voice by Performance Sampling and Spectral Models' at mtg.upf.edu, a 2007 journal article in the w:IEEE Signal Processing Society's Signal Processing Magazine
- 'Speech-to-Singing Synthesis: Converting Speaking Voices to Singing Voices by Controlling Acoustic Features Unique to Singing Voices' at researchgate.net, a November 2007 paper published in the IEEE conference on Applications of Signal Processing to Audio and Acoustics
Timeline of synthetic human-like fakes
See the #SSFWIKI Mediatheque for viewing media that is or is probably to do with synthetic human-like fakes.
2020's synthetic human-like fakes
- 2023 | Real-time digital look-and-sound-alike crime | In April a man in northern China was defrauded of 4.3 million yuan by a criminal employing a digital look-and-sound-alike pretending to be his friend on a video call made with a stolen messaging service account.[3]
- 2023 | Election meddling with digital look-alikes | The w:2023 Turkish presidential election saw numerous deepfake controversies.
- "Ahead of the election in Turkey, President Recep Tayyip Erdogan showed a video linking his main challenger Kemal Kilicdaroglu to the militant Kurdish organization PKK." [...] "Research by DW's fact-checking team in cooperation with DW's Turkish service shows that the video at the campaign rally was manipulated by combining two separate videos with totally different backgrounds and content." reports dw.com
- 2023 | March 7 th | science / demonstration | Microsoft researchers submitted a paper for publication outlining their Cross-lingual neural codec language modeling system at arxiv.org dubbed VALL-E X at microsoft.com, that extends upon VALL-E's capabilities to be cross-lingual and also maintaining the same "emotional tone" from sample to fake.
- 2023 | January 5th | science / demonstration | Microsoft researchers announced VALL-E - Neural Codec Language Models are Zero-Shot Text to Speech Synthesizers (at microsoft.com) that is able to thieve a voice from only 3 seconds of sample and it is also able to mimic the "emotional tone" of the sample the synthesis if produced of.[20]
- 2023 | January 1st | Law | Law on sexual offences in Finland 2023 is found in Chapter 20 of the Finnish Criminal Code titled "Seksuaalirikoksista" ("Sexual offences") and came into effect on Sunday 2023-01-01.[21]
The new law in Finland protects adults against sexual image based abuse be it real or synthetic in origin.
Other countries have also woken up to the problems of synthesis crime and have legislated laws against synthesis and other related crimes.
Relevant sections of Chapter 20
- 7 § Non-consensual dissemination of a sexual image criminalizes distribution of unauthorized real and synthetic sexual images without permission. (7 § Seksuaalisen kuvan luvaton levittäminen[21])
- 19 § Distribution of an image depicting a child in a sexual manner [21] criminalizes the distribution of real and synthetic child sexual abuse material (CSAM). Attempting this crime is also punishable. (19 § Lasta seksuaalisesti esittävän kuvan levittäminen[21])
- 20 § Aggravated distribution of an image depicting a child in a sexual manner [21] defines the parameters for aggravated form of the crime of making CSAM available. (20 § Törkeä lasta seksuaalisesti esittävän kuvan levittäminen[21])
- 21 § Possession of an image depicting a child in a sexual manner[21] criminalizes the possession of CSAM and acquiring access for the intent to access CSAM. (21 § Lasta seksuaalisesti esittävän kuvan hallussapito)[21])
This 2023 upgrade and gather-together of the Finnish Criminal Code on sexual offences was made upon the initiative of the 2019-2023 w:Marin Cabinet, was voted into law by the w:Members of the Parliament of Finland, 2019–2023 and it came into effect on Sunday 2023-01-01.
Translation to English by the Ministry of Justice: Criminal Code (39/1889) - Chapter 20 - Sexual offences (translation) as .pdf at oikeusministerio.fi (subject to possible revisions)
- 2022 | science and demonstration | w:OpenAI(.com) published w:ChatGPT, a discutational AI accessible with a free account at chat.openai.com. Initial version was published on 2022-11-30.
- 2022 | brief report of counter-measures | Protecting world leaders against deep fakes using facial, gestural, and vocal mannerisms is a brief report by Matyáš Boháček and Hany Farid on their recent work published on Wednesday 2022-11-23 in w:Proceedings of the National Academy of Sciences of the United States of America (PNAS). 'Protecting world leaders against deep fakes using facial, gestural, and vocal mannerisms' at pnas.org[1] Publication date 2022-11-23.
- 2022 | counter-measure | Detecting deep-fake audio through vocal tract reconstruction is an epic scientific work, against fake human-like voices, from the w:University of Florida in published to peers in August 2022.


The work Who Are You (I Really Wanna Know)? Detecting Audio DeepFakes Through Vocal Tract Reconstruction at usenix.org, presentation page, version included in the proceedings[8] and slides from researchers of the Florida Institute for Cybersecurity Research (FICS) at fics.institute.ufl.edu in the w:University of Florida received funding from the w:Office of Naval Research and was presented on 2022-08-11 at the 31st w:USENIX Security Symposium.
This work was done by PhD student Logan Blue, Kevin Warren, Hadi Abdullah, Cassidy Gibson, Luis Vargas, Jessica O’Dell, Kevin Butler and Professor Patrick Traynor.
The University of Florida Research Foundation Inc has filed for and received an US patent titled 'Detecting deep-fake audio through vocal tract reconstruction' registration number US20220036904A1 (link to patents.google.com) with 20 claims. The patent application was published on Thursday 2022-02-03. The patent application was approved on 2023-07-04 and has an adjusted expiration date of Sunday 2041-12-29.
- PhD student Logan Blue and professor Patrick Traynor wrote an article for the general public on the work titled Deepfake audio has a tell – researchers use fluid dynamics to spot artificial imposter voices at theconversation.com[9] that was published Tuesday 2022-09-20 and permanently w:copylefted it under Creative Commons Attribution-NoDerivatives (CC-BY-ND).. Presented to peers in August 2022 and to the general public in September 2022.
- 2022 | disinformation attack | In June 2022 a fake digital look-and-sound-alike in the appearance and voice of w:Vitali Klitschko, mayor of w:Kyiv, held fake video phone calls with several European mayors. The Germans determined that the video phone call was fake by contacting the Ukrainian officials. This attempt at covert disinformation attack was originally reported by w:Der Spiegel.[22][23]
- 2022 | science | w:DALL-E 2, a successor designed to generate more realistic images at higher resolutions that "can combine concepts, attributes, and styles" was published in April 2022.[24] (Wikipedia)
- 2022 | counter-measure | Protecting President Zelenskyy against deep fakes 'Protecting President Zelenskyy against Deep Fakes' at arxiv.org[25] by Matyáš Boháček of Johannes Kepler Gymnasium and w:Hany Farid, the dean and head of of w:Berkeley School of Information at the University of California, Berkeley. This brief paper describes their automated digital look-alike detection system and evaluate its efficacy and reliability in comparison to humans with untrained eyes. Their work provides automated evaluation tools to catch so called "deep fakes" and their motivation seems to have been to find automation armor against disinformation warfare against humans and the humanity. Automated digital media forensics is a very good idea explored by many. Boháček and Farid 2022 detection system works by evaluating both facial mannerisms as well as gestural mannerisms to detect the non-human ones from the ones that are human in origin. Preprint published in February 2022 and submitted to w:arXiv in June 2022
- 2022 | science / review of counter-measures | 'A Review of Modern Audio Deepfake Detection Methods: Challenges and Future Directions' at mdpi.com[26], a review of audio deepfake detection methods by researchers Zaynab Almutairi and Hebah Elgibreen of the w:King Saud University, Saudi Arabia published in w:Algorithms (journal) on Wednesday 2022-05-04 published by the w:MDPI (Multidisciplinary Digital Publishing Institute). This article belongs to the Special Issue Commemorative Special Issue: Adversarial and Federated Machine Learning: State of the Art and New Perspectives at mdpi.com
- 2022 | science / counter-measure | 'Attacker Attribution of Audio Deepfakes' at arxiv.org, a pre-print was presented at the Interspeech 2022 conference organized by w:International Speech Communication Association in Korea September 18-22 2022.
- 2021 | Science and demonstration | In the NeurIPS 2021 held virtually in December researchers from Nvidia and w:Aalto University present their paper Alias-Free Generative Adversarial Networks (StyleGAN3) at nvlabs.github.io and associated implementation in w:PyTorch and the results are deceivingly human-like in appearance. StyleGAN3 paper as .pdf at nvlabs-fi-cdn.nvidia.com
- 2021 | Entertainment | The Swedish pop band w:ABBA published an album in September and will be performing shows where the music is live and real, but the visuals will be rejuvenated digital look-alikes of the band members displayed to the fans with w:holography technology. ABBA used w:Industrial Light & Magic as the purveyor of technology. w:Industrial Light & Magic was acquired by w:The Walt Disney Company in 2012 as part of their acquisition w:Lucasfilm.
- 2021 | Controversy | July 2021 saw the release of w:Roadrunner: A Film About Anthony Bourdain and soon controversy arose, as the director w:Morgan Neville admitted to w:Helen Rosner, a food writer for w:The New Yorker that he had contracted an AI company to thieve w:Anthony Bourdain's voice and used it to insert audio that sounded like him, without declaring it as faked.[27][1st seen in 5]
- 2021 | Science | Voice Cloning: a Multi-Speaker Text-to-Speech Synthesis Approach based on Transfer Learning .pdf at arxiv.org, a paper submitted in Feb 2021 by researchers from the w:University of Turin.[1st seen in 6]
- 2021 | crime / fraud | Template loop detected: Synthetic human-like fakes
- 2021 | science and demonstration | DALL-E, a w:deep learning model developed by w:OpenAI to generate digital images from w:natural language descriptions, called "prompts" was published in January 2021. DALL-E uses a version of w:GPT-3 modified to generate images. (Adapted from Wikipedia)
- 2020 | counter-measure | The 'AI Incident Database' at incidentdatabase.ai was introduced on 2020-11-18 by the w:Partnership on AI.[28]
- 2020 | Controversy / Public service announcement | Channel 4 thieved the appearance of Queen Elizabeth II using deepfake methods. The product of synthetic human-like fakery originally aired on Channel 4 on 25 December at 15:25 GMT.[29] View in YouTube
- 2020 | reporting | "Deepfake porn is now mainstream. And major sites are cashing in" at wired.co.uk by Matt Burgess. Published August 2020.
- 2020 | demonstration | Moondisaster.org (full film embedded in website) project by the Center for Advanced Virtuality of the w:MIT published in July 2020, makes use of various methods of making a synthetic human-like fake. Alternative place to watch: In Event of Moon Disaster - FULL FILM at youtube.com
- 2020 | US state law | January 1 2020 [30] the w:California w:US state law "AB-602 Depiction of individual using digital or electronic technology: sexually explicit material: cause of action." came into effect in the civil code of the w:California Codes banning the manufacturing and w:digital distribution of synthetic pornography without the w:consent of the people depicted. AB-602 provides victims of synthetic pornography with w:injunctive relief and poses legal threats of w:statutory and w:punitive damages on w:criminals making or distributing synthetic pornography without consent. The bill AB-602 was signed into law by California w:Governor w:Gavin Newsom on October 3 2019 and was authored by w:California State Assemblymember w:Marc Berman and an identical Senate bill was coauthored by w:California Senator w:Connie Leyva.[31][32] AB602 at trackbill.com
 Homie w:Marc Berman, a righteous fighter for our human rights in this age of industrial disinformation filth and an Assemblymember of the w:California State Assembly, most loved for authoring AB-602 - Depiction of individual using digital or electronic technology: sexually explicit material: cause of action, which came into effect on Jan 1 2020, banning both the manufacturing and w:digital distribution of synthetic pornography without the w:consent of the people depicted.
Homie w:Marc Berman, a righteous fighter for our human rights in this age of industrial disinformation filth and an Assemblymember of the w:California State Assembly, most loved for authoring AB-602 - Depiction of individual using digital or electronic technology: sexually explicit material: cause of action, which came into effect on Jan 1 2020, banning both the manufacturing and w:digital distribution of synthetic pornography without the w:consent of the people depicted.
- 2020 | Chinese legislation | On Wednesday January 1 2020 Chinese law requiring that synthetically faked footage should bear a clear notice about its fakeness came into effect. Failure to comply could be considered a w:crime the w:Cyberspace Administration of China (cac.gov.cn) stated on its website. China announced this new law in November 2019.[33] The Chinese government seems to be reserving the right to prosecute both users and w:online video platforms failing to abide by the rules. [34]
2010's synthetic human-like fakes
- 2019 | science and demonstration | At the December 2019 NeurIPS conference, a novel method for making animated fakes of anything with AI First Order Motion Model for Image Animation (website at aliaksandrsiarohin.github.io), (paper) (github) was presented.[1st seen in 7]
- Reporting Memers are making deepfakes, and things are getting weird at technologyreview.com, 2020-08-28 by Karen Hao.
- 2019 | demonstration | In September 2019 w:Yle, the Finnish w:public broadcasting company, aired a result of experimental w:journalism, a deepfake of the President in office w:Sauli Niinistö in its main news broadcast for the purpose of highlighting the advancing disinformation technology and problems that arise from it.
- 2019 | US state law | On September 1 2019 w:Texas Senate bill SB 751 - Relating to the creation of a criminal offense for fabricating a deceptive video with intent to influence the outcome of an election w:amendments to the election code came into effect in the w:Law of Texas, giving w:candidates in w:elections a 30-day protection period to the elections during which making and distributing digital look-alikes or synthetic fakes of the candidates is an offense. The law text defines the subject of the law as "a video, created with the intent to deceive, that appears to depict a real person performing an action that did not occur in reality"[35] SB 751 was introduced to the Senate by w:Bryan Hughes (politician).[36]
- 2019 | US state law | Since July 1 2019[37] w:Virginia w:has criminalized the sale and dissemination of unauthorized synthetic pornography, but not the manufacture.[38], as section § 18.2-386.2 titled 'Unlawful dissemination or sale of images of another; penalty.' became part of the w:Code of Virginia.
 Homie w:Marcus Simon (marcussimon.com) is a Member of the w:Virginia House of Delegates and a true pioneer in legislating against synthetic filth.
Homie w:Marcus Simon (marcussimon.com) is a Member of the w:Virginia House of Delegates and a true pioneer in legislating against synthetic filth.
Code of Virginia (TOC) » Title 18.2. Crimes and Offenses Generally » Chapter 8. Crimes Involving Morals and Decency » Article 5. Obscenity and Related Offenses » Section § 18.2-386.2. Unlawful dissemination or sale of images of another; penalty
The section § 18.2-386.2. Unlawful dissemination or sale of images of another; penalty. of Virginia is as follows:
A. Any w:person who, with the w:intent to w:coerce, w:harass, or w:intimidate, w:maliciously w:disseminates or w:sells any videographic or still image created by any means whatsoever that w:depicts another person who is totally w:nude, or in a state of undress so as to expose the w:genitals, pubic area, w:buttocks, or female w:breast, where such person knows or has reason to know that he is not w:licensed or w:authorized to disseminate or sell such w:videographic or w:still image is w:guilty of a Class 1 w:misdemeanor.
- For purposes of this subsection, "another person" includes a person whose image was used in creating, adapting, or modifying a videographic or still image with the intent to depict an actual person and who is recognizable as an actual person by the person's w:face, w:likeness, or other distinguishing characteristic.
B. If a person uses w:services of an w:Internet service provider, an electronic mail service provider, or any other information service, system, or access software provider that provides or enables computer access by multiple users to a computer server in committing acts prohibited under this section, such provider shall not be held responsible for violating this section for content provided by another person.
C. Venue for a prosecution under this section may lie in the w:jurisdiction where the unlawful act occurs or where any videographic or still image created by any means whatsoever is produced, reproduced, found, stored, received, or possessed in violation of this section.
D. The provisions of this section shall not preclude prosecution under any other w:statute.[38]
The identical bills were House Bill 2678 presented by w:Delegate w:Marcus Simon to the w:Virginia House of Delegates on January 14 2019 and three day later an identical Senate bill 1736 was introduced to the w:Senate of Virginia by Senator w:Adam Ebbin.
- 2019 | Science | Sample Efficient Adaptive Text-to-Speech .pdf at arxiv.org, a 2019 paper from Google researchers, published as a conference paper at w:International Conference on Learning Representations (ICLR)[1st seen in 6]
- 2019 | science and demonstration | 'Speech2Face: Learning the Face Behind a Voice' at arXiv.org a system for generating likely facial features based on the voice of a person, presented by the w:MIT Computer Science and Artificial Intelligence Laboratory at the 2019 w:CVPR. Speech2Face at github.com This may develop to something that really causes problems. "Speech2Face: Neural Network Predicts the Face Behind a Voice" reporing at neurohive.io, "Speech2Face Sees Voices and Hears Faces: Dreams Come True with AI" reporting at belitsoft.com
- 2019 | crime | w:Fraud with digital sound-alike technology surfaced in 2019. See 'An artificial-intelligence first: Voice-mimicking software reportedly used in a major theft', a 2019 Washington Post article or 'A Voice Deepfake Was Used To Scam A CEO Out Of $243,000' at Forbes.com (2019-09-03)
- 2019 | demonstration | 'Which Face is real?' at whichfaceisreal.com is an easily unnerving game by Carl Bergstrom and Jevin West where you need to try to distinguish from a pair of photos which is real and which is not. A part of the "tools" of the Calling Bullshit course taught at the w:University of Washington. Relevancy: certain
- 2019 | demonstration | 'Thispersondoesnotexist.com' (since February 2019) by Philip Wang. It showcases a w:StyleGAN at the task of making an endless stream of pictures that look like no-one in particular, but are eerily human-like. Relevancy: certain
- 2019 | action | w:Nvidia w:open sources w:StyleGAN, a novel w:generative adversarial network.[39]
- 2018 | counter-measure | In September 2018 Google added “involuntary synthetic pornographic imagery” to its ban list, allowing anyone to request the search engine block results that falsely depict them as “nude or in a sexually explicit situation.”[40] Information on removing involuntary fake pornography from Google at support.google.com if it shows up in Google and the form to request removing involuntary fake pornography at support.google.com, select "I want to remove: A fake nude or sexually explicit picture or video of myself"

- 2018 | science and demonstration | The work 'Transfer Learning from Speaker Verification to Multispeaker Text-To-Speech Synthesis' (at arXiv.org) was presented at the 2018 w:Conference on Neural Information Processing Systems (NeurIPS). The pre-trained model is able to steal voices from a sample of only 5 seconds with almost convincing results.
- 2018 | science | Progressive Growing of GANs for Improved Quality, Stability, and Variation at arxiv.org (.pdf), colloquially known as ProGANs were presented by Nvidia researchers at the 2018 ICLR. w:International Conference on Learning Representations
- 2018 | demonstration | At the 2018 w:World Internet Conference in w:Wuzhen the w:Xinhua News Agency presented two digital look-alikes made to the resemblance of its real news anchors Qiu Hao (w:Chinese language)[41] and Zhang Zhao (w:English language). The digital look-alikes were made in conjunction with w:Sogou.[42] Neither the w:speech synthesis used nor the gesturing of the digital look-alike anchors were good enough to deceive the watcher to mistake them for real humans imaged with a TV camera.
- 2018 | action | Deep Fakes letter to the Office of the Director of National Intelligence at schiff.house.gov, a letter sent to the w:Director of National Intelligence on 2018-09-13 by congresspeople w:Adam Schiff, w:Stephanie Murphy and w:Carlos Curbelo requesting a report be compiled on the synthetic human-like fakes situation and what are the threats and what could be the solutions.[1st seen in 8]
- 2018 | controversy / demonstration | The w:deepfakes controversy surfaces where porn videos were doctored utilizing w:deep machine learning so that the face of the actress was replaced by the software's opinion of what another persons face would look like in the same pose and lighting.
- 2017 | science | 'Synthesizing Obama: Learning Lip Sync from Audio' at grail.cs.washington.edu. In SIGGRAPH 2017 by Supasorn Suwajanakorn et al. of the w:University of Washington presented an audio driven digital look-alike of upper torso of Barack Obama. It was driven only by a voice track as source data for the animation after the training phase to acquire w:lip sync and wider facial information from w:training material consisting 2D videos with audio had been completed.[43] Relevancy: certain
- 2016 | movie | w:Rogue One is a Star Wars film for which digital look-alikes of actors w:Peter Cushing and w:Carrie Fisher were made. In the film their appearance would appear to be of same age as the actors were during the filming of the original 1977 w:Star Wars (film) film.
- 2016 | science / demonstration | w:DeepMind's w:WaveNet owned by w:Google also demonstrated ability to steal people's voices

- 2016 | science and demonstration | w:Adobe Inc. publicly demonstrates w:Adobe Voco, a sound-like-anyone machine '#VoCo. Adobe Audio Manipulator Sneak Peak with Jordan Peele | Adobe Creative Cloud' on Youtube. THe original Adobe Voco required 20 minutes of sample to thieve a voice. Relevancy: certain.
- 2016 | science | 'Face2Face: Real-time Face Capture and Reenactment of RGB Videos' at Niessnerlab.org A paper (with videos) on the semi-real-time 2D video manipulation with gesture forcing and lip sync forcing synthesis by Thies et al, Stanford. Relevancy: certain
- 2016 | music video | 'Plug' by Kube at youtube.com - A 2016 music video by w:Kube (rapper) (w:fi:Kube), that shows deepfake-like technology this early. Video was uploaded on 2016-09-15 and is directed by Faruk Nazeri.
- 2015 | Science | 'Deep Learning Face Attributes in the Wild' at arxiv.org presented at the 2015 w:International Conference on Computer Vision
- 2015 | movie | In the w:Furious 7 a digital look-alike made of the actor w:Paul Walker who died in an accident during the filming was done by w:Weta Digital to enable the completion of the film.[44]
- 2014 | science | w:Ian Goodfellow et al. presented the principles of a w:generative adversarial network. GANs made the headlines in early 2018 with the w:deepfakes controversies.
- 2013 | demonstration | At the 2013 SIGGGRAPH w:Activision and USC presented a w:real time computing "Digital Ira" a digital face look-alike of Ari Shapiro, an ICT USC research scientist,[45] utilizing the USC light stage X by Ghosh et al. for both reflectance field and motion capture.[46] The end result both precomputed and real-time rendering with the modernest game w:GPU shown here and looks fairly realistic.
- 2013 | demonstration | A 'Scanning and Printing a 3D Portrait of President Barack Obama' at ict.usc.edu. A 7D model and a 3D bust was made of President Obama with his consent. Relevancy: Relevancy: certain
- 2011 | Law in Finland | Distribution and attempt of distribution and also possession of synthetic CSAM was criminalized on Wednesday 2011-06-01, upon the initiative of the w:Vanhanen II Cabinet. These protections against CSAM were moved into 19 §, 20 § and 21 § of Chapter 20 when the Law on sexual offences in Finland 2023 was improved and gathered into Chapter 20 upon the initiative of the w:Marin Cabinet.
2000's synthetic human-like fakes
- 2010 | movie | w:Walt Disney Pictures released a sci-fi sequel entitled w:Tron: Legacy with a digitally rejuvenated digital look-alike made of the actor w:Jeff Bridges playing the w:antagonist w:CLU.
- 2009 | movie | A digital look-alike of a younger w:Arnold Schwarzenegger was made for the movie w:Terminator Salvation though the end result was critiqued as unconvincing. Facial geometry was acquired from a 1984 mold of Schwarzenegger.
- 2009 | demonstration | Paul Debevec: 'Animating a photo-realistic face' at ted.com Debevec et al. presented new digital likenesses, made by w:Image Metrics, this time of actress w:Emily O'Brien whose reflectance was captured with the USC light stage 5. At 00:04:59 you can see two clips, one with the real Emily shot with a real camera and one with a digital look-alike of Emily, shot with a simulation of a camera - Which is which is difficult to tell. Bruce Lawmen was scanned using USC light stage 6 in still position and also recorded running there on a w:treadmill. Many, many digital look-alikes of Bruce are seen running fluently and natural looking at the ending sequence of the TED talk video. [47] Motion looks fairly convincing contrasted to the clunky run in the w:Animatrix: Final Flight of the Osiris which was w:state-of-the-art in 2003 if photorealism was the intention of the w:animators.
- 2004 | movie | The w:Spider-man 2 (and w:Spider-man 3, 2007) films. Relevancy: The films include a digital look-alike made of actor w:Tobey Maguire by w:Sony Pictures Imageworks.[48]
- 2003 | short film | w:The Animatrix: Final Flight of the Osiris a w:state-of-the-art want-to-be human likenesses not quite fooling the watcher made by w:Square Pictures.


An analytical BRDF must take into account the subsurface scattering, or the end result will not pass human testing.
- 2003 | movie(s) | The w:Matrix Reloaded and w:Matrix Revolutions films. Relevancy: First public display of digital look-alikes that are virtually indistinguishable from the real actors. 'Universal Capture - Image-based Facial Animation for "The Matrix Reloaded"' at researchgate.net (2003)
- 2002 | music video | 'Bullet' by Covenant on Youtube by w:Covenant (band) from their album w:Northern Light (Covenant album). Relevancy: Contains the best upper-torso digital look-alike of Eskil Simonsson (vocalist) that their organization could procure at the time. Here you can observe the classic "skin looks like cardboard"-bug (assuming this was not intended) that thwarted efforts to make digital look-alikes that pass human testing before the reflectance capture and dissection in 1999 by w:Paul Debevec et al. at the w:University of Southern California and subsequent development of the "Analytical w:BRDF" (quote-unquote) by ESC Entertainment, a company set up for the sole purpose of making the cinematography for the 2003 films Matrix Reloaded and Matrix Revolutions possible, lead by George Borshukov.
1990's synthetic human-like fakes

- 1999 | science | 'Acquiring the reflectance field of a human face' paper at dl.acm.org w:Paul Debevec et al. of w:USC did the first known reflectance capture over the human face with their extremely simple w:light stage. They presented their method and results in w:SIGGRAPH 2000. The scientific breakthrough required finding the w:subsurface light component (the simulation models are glowing from within slightly) which can be found using knowledge that light that is reflected from the oil-to-air layer retains its w:Polarization (waves) and the subsurface light loses its polarization. So equipped only with a movable light source, movable video camera, 2 polarizers and a computer program doing extremely simple math and the last piece required to reach photorealism was acquired.[6]
- 1999 | institute founded | The w:Institute for Creative Technologies was founded by the w:United States Army in the w:University of Southern California. It collaborates with the w:United States Army Futures Command, w:United States Army Combat Capabilities Development Command, w:Combat Capabilities Development Command Soldier Center and w:United States Army Research Laboratory.[49]. In 2016 w:Hao Li was appointed to direct the institute.
- 1997 | technology / science | 'Video rewrite: Driving visual speech with audio' at www2.eecs.berkeley.edu[2][1st seen in 9] Christoph Breigler, Michelle Covell and Malcom Slaney presented their work at the ACM SIGGRAPH 1997. Download video evidence of Video rewrite: Driving visual speech with audio Bregler et al 1997 from dropbox.com, view author's site at chris.bregler.com, paper at dl.acm.org paper at researchgate.net
- 1994 | movie | w:The Crow (1994 film) was the first film production to make use of w:digital compositing of a computer simulated representation of a face onto scenes filmed using a w:body double. Necessity was the muse as the actor w:Brandon Lee portraying the protagonist was tragically killed accidentally on-stage.
1970's synthetic human-like fakes
- 1976 | movie | w:Futureworld reused parts of A Computer Animated Hand on the big screen.
- 1972 | entertainment | 'A Computer Animated Hand' on Vimeo. w:A Computer Animated Hand by w:Edwin Catmull and w:Fred Parke. Relevancy: This was the first time that w:computer-generated imagery was used in film to animate moving human-like appearance.
- 1971 | science | 'Images de synthèse : palme de la longévité pour l’ombrage de Gouraud' (still photos). w:Henri Gouraud (computer scientist) made the first w:Computer graphics w:geometry w:digitization and representation of a human face. Modeling was his wife Sylvie Gouraud. The 3D model was a simple w:wire-frame model and he applied w:Gouraud shading to produce the first known representation of human-likeness on computer. [50]
1960's synthetic human-like fakes
- 1961 | demonstration | The first singing by a computer was performed by an w:IBM 704 and the song was w:Daisy Bell, written in 1892 by British songwriter w:Harry Dacre. Go to Mediatheque#1961 to view.
1930's synthetic human-like fakes
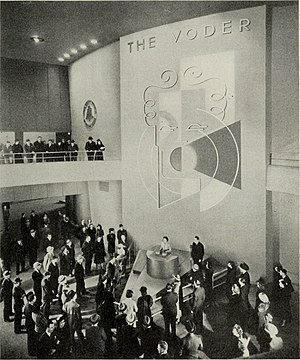
- 1939 | demonstration | w:Voder (Voice Operating Demonstrator) from the w:Bell Telephone Laboratory was the first time that w:speech synthesis was done electronically by breaking it down into its acoustic components. It was invented by w:Homer Dudley in 1937–1938 and developed on his earlier work on the w:vocoder. (Wikipedia)
1770's synthetic human-like fakes

- 1791 | science | w:Wolfgang von Kempelen's Speaking Machine of w:Wolfgang von Kempelen of w:Pressburg, w:Hungary, described in a 1791 paper was w:bellows-operated.[51] This machine added models of the tongue and lips, enabling it to produce w:consonants as well as w:vowels. (based on w:Speech synthesis#History)
- 1779 | science / discovery | w:Christian Gottlieb Kratzenstein won the first prize in a competition announced by the w:Russian Academy of Sciences for models he built of the human w:vocal tract that could produce the five long w:vowel sounds.[52] (Based on w:Speech synthesis#History)
Footnotes
- ↑ It is terminologically more precise, more inclusive and more useful to talk about 'terroristic synthetic pornography', if we want to talk about things with their real names, than 'synthetic rape porn', because also synthesizing recordings of consentual looking sex scenes can be terroristic in intent.
- ↑ Whether a suspect can defend against faked synthetic speech that sounds like him/her depends on how up-to-date the judiciary is. If no information and instructions about digital sound-alikes have been given to the judiciary, they likely will not believe the defense of denying that the recording is of the suspect's voice.
Contact information of organizations
Please contact these organizations and tell them to work harder against the disinformation weapons
1st seen in
- ↑ 1.0 1.1 https://www.reddit.com/r/VocalSynthesis/
- ↑ 2.0 2.1 2.2 2.3 2.4 2.5 https://wordlift.io/blog/en/best-plagiarism-checkers-for-ai-generated-content/
- ↑ https://www.ucl.ac.uk/news/2016/aug/new-computer-programme-replicates-handwriting via Google search for "ai handwriting generator"
- ↑ https://seanvasquez.com/handwriting-generation redirects to Calligrapher.ai - seen in https://www.reddit.com/r/MachineLearning/comments/gh9cbg/p_generate_handwriting_with_an_inbrowser/
- ↑ Witness newsletter I subscribed to at https://www.witness.org/get-involved/
- ↑ 6.0 6.1 https://www.connectedpapers.com/main/8fc09dfcff78ac9057ff0834a83d23eb38ca198a/Transfer-Learning-from-Speaker-Verification-to-Multispeaker-TextToSpeech-Synthesis/graph
- ↑ https://www.technologyreview.com/2020/08/28/1007746/ai-deepfakes-memes/
- ↑ 'US Lawmakers: AI-Generated Fake Videos May Be a Security Threat' at uk.pcmag.com, 2018-09-13 reporting by Michael Kan
- ↑ PROTECTING PRESIDENT ZELENSKYY AGAINST DEEP FAKES https://arxiv.org/pdf/2206.12043.pdf
References
- ↑ 1.0 1.1 1.2 Boháček, Matyáš; Farid, Hany (2022-11-23). "Protecting world leaders against deep fakes using facial, gestural, and vocal mannerisms". w:Proceedings of the National Academy of Sciences of the United States of America. 119 (48). doi:10.1073/pnas.221603511. Retrieved 2023-01-05.
- ↑ 2.0 2.1 2.2 Bregler, Christoph; Covell, Michele; Slaney, Malcolm (1997-08-03). "Video Rewrite: Driving Visual Speech with Audio" (PDF). SIGGRAPH '97: Proceedings of the 24th annual conference on Computer graphics and interactive techniques: 353–360. doi:10.1145/258734.258880. Retrieved 2022-09-09.
- ↑ 3.0 3.1 3.2 "'Deepfake' scam in China fans worries over AI-driven fraud". w:Reuters.com. w:Reuters. 2023-05-22. Retrieved 2023-06-05.
- ↑ https://www.washingtonpost.com/technology/2019/09/04/an-artificial-intelligence-first-voice-mimicking-software-reportedly-used-major-theft/
- ↑
"You Won't Believe What Obama Says In This Video!". w:YouTube. w:BuzzFeed. 2018-04-17. Retrieved 2022-01-05.
We're entering an era in which our enemies can make anyone say anything at any point in time.
- ↑ 6.0 6.1 Debevec, Paul (2000). "Acquiring the reflectance field of a human face". Proceedings of the 27th annual conference on Computer graphics and interactive techniques - SIGGRAPH '00. ACM. pp. 145–156. doi:10.1145/344779.344855. ISBN 978-1581132083. Retrieved 2020-06-27.
- ↑ 7.0 7.1 "Inventing Entertainment: The Early Motion Pictures and Sound Recordings of the Edison Companies". Memory.loc.gov. w:Library of Congress. Retrieved 2020-12-09.
- ↑ 8.0 8.1 Blue, Logan; Warren, Kevin; Abdullah, Hadi; Gibson, Cassidy; Vargas, Luis; O’Dell, Jessica; Butler, Kevin; Traynor, Patrick (August 2022). "Detecting deep-fake audio through vocal tract reconstruction". Proceedings of the 31st USENIX Security Symposium: 2691–2708. ISBN 978-1-939133-31-1. Retrieved 2022-10-06.
- ↑ 9.0 9.1
Blue, Logan; Traynor, Patrick (2022-09-20). "Deepfake audio has a tell – researchers use fluid dynamics to spot artificial imposter voices". theconversation.com. w:The Conversation (website). Retrieved 2022-10-05.
By estimating the anatomy responsible for creating the observed speech, it’s possible to identify the whether the audio was generated by a person or a computer.
- ↑ 10.0 10.1
Drew, Harwell (2020-04-16). "An artificial-intelligence first: Voice-mimicking software reportedly used in a major theft". w:washingtonpost.com. w:Washington Post. Retrieved 2019-07-22.
Researchers at the cybersecurity firm Symantec said they have found at least three cases of executives’ voices being mimicked to swindle companies. Symantec declined to name the victim companies or say whether the Euler Hermes case was one of them, but it noted that the losses in one of the cases totaled millions of dollars.
- ↑ 11.0 11.1 Stupp, Catherine (2019-08-30). "Fraudsters Used AI to Mimic CEO's Voice in Unusual Cybercrime Case". w:wsj.com. w:The Wall Street Journal. Retrieved 2022-01-01.
- ↑ 12.0 12.1
Damiani, Jesse (2019-09-03). "A Voice Deepfake Was Used To Scam A CEO Out Of $243,000". w:Forbes.com. w:Forbes. Retrieved 2022-01-01.
According to a new report in The Wall Street Journal, the CEO of an unnamed UK-based energy firm believed he was on the phone with his boss, the chief executive of firm’s the German parent company, when he followed the orders to immediately transfer €220,000 (approx. $243,000) to the bank account of a Hungarian supplier. In fact, the voice belonged to a fraudster using AI voice technology to spoof the German chief executive. Rüdiger Kirsch of Euler Hermes Group SA, the firm’s insurance company, shared the information with WSJ.
- ↑ "Fake voices 'help cyber-crooks steal cash'". w:bbc.com. w:BBC. 2019-07-08. Retrieved 2020-07-22.
- ↑ Franceschi-Bicchierai, Lorenzo (2020-07-23). "Listen to This Deepfake Audio Impersonating a CEO in Brazen Fraud Attempt". w:Vice.com. w:Vice (magazine). Retrieved 2022-01-03.
- ↑ 15.0 15.1 https://www.forbes.com/sites/thomasbrewster/2021/10/14/huge-bank-fraud-uses-deep-fake-voice-tech-to-steal-millions/
- ↑ Flatow, Ira (April 4, 2008). "1860 'Phonautograph' Is Earliest Known Recording". NPR. Retrieved 2012-12-09.
- ↑ https://www.theverge.com/2023/2/7/23587454/microsoft-bing-edge-chatgpt-ai
- ↑ https://www.reddit.com/r/MachineLearning/comments/gh9cbg/p_generate_handwriting_with_an_inbrowser/
- ↑ "What is IWR? (Intelligent Word Recognition)". eFileCabinet. 2016-01-04. Retrieved 2021-09-21.
- ↑
Edwards, Benj (2023-01-10). "Microsoft's new AI can simulate anyone's voice with 3 seconds of audio". w:Arstechnica.com. Arstechnica. Retrieved 2023-05-05.
For the paper's conclusion, they write: "Since VALL-E could synthesize speech that maintains speaker identity, it may carry potential risks in misuse of the model, such as spoofing voice identification or impersonating a specific speaker. To mitigate such risks, it is possible to build a detection model to discriminate whether an audio clip was synthesized by VALL-E. We will also put Microsoft AI Principles into practice when further developing the models."
- ↑ 21.0 21.1 21.2 21.3 21.4 21.5 21.6 21.7
Authoritative up-to-date version of the Criminal Code chapter 20 On sexual offences can always be found at finlex.fi
Translation to English by the Ministry of Justice: Criminal Code (39/1889) - Chapter 20 - Sexual offences (translation) as .pdf at oikeusministerio.fi (subject to possible revisions) - ↑ https://www.theguardian.com/world/2022/jun/25/european-leaders-deepfake-video-calls-mayor-of-kyiv-vitali-klitschko
- ↑ https://www.dw.com/en/vitali-klitschko-fake-tricks-berlin-mayor-in-video-call/a-62257289
- ↑ "DALL·E 2". OpenAI. Retrieved 2023-04-22.
- ↑ Boháček, Matyáš; Farid, Hany (2022-06-14). "Protecting President Zelenskyy against Deep Fakes". arXiv:2206.12043 [cs.CV].
- ↑
Almutairi, Zaynab; Elgibreen, Hebah (2022-05-04). "A Review of Modern Audio Deepfake Detection Methods: Challenges and Future Directions". w:Algorithms (journal). doi:https://doi.org/10.3390/a15050155 Check
|doi=value (help). Retrieved 2022-10-18. - ↑
Rosner, Helen (2021-07-15). "A Haunting New Documentary About Anthony Bourdain". w:The New Yorker. Retrieved 2021-08-25. Check
|author-link=value (help) - ↑ https://www.partnershiponai.org/aiincidentdatabase/
- ↑ https://www.bbc.com/news/technology-55424730
- ↑ Johnson, R.J. (2019-12-30). "Here Are the New California Laws Going Into Effect in 2020". KFI. iHeartMedia. Retrieved 2021-01-23.
- ↑ "AB 602 - California Assembly Bill 2019-2020 Regular Session - Depiction of individual using digital or electronic technology: sexually explicit material: cause of action". openstates.org. openstates.org. Retrieved 2021-03-24.
- ↑ Mihalcik, Carrie (2019-10-04). "California laws seek to crack down on deepfakes in politics and porn". w:cnet.com. w:CNET. Retrieved 2021-01-23.
- ↑ "China seeks to root out fake news and deepfakes with new online content rules". w:Reuters.com. w:Reuters. 2019-11-29. Retrieved 2021-01-23.
- ↑ Statt, Nick (2019-11-29). "China makes it a criminal offense to publish deepfakes or fake news without disclosure". w:The Verge. Retrieved 2021-01-23.
- ↑
"Relating to the creation of a criminal offense for fabricating a deceptive video with intent to influence the outcome of an election". w:Texas. 2019-06-14. Retrieved 2021-01-23.
In this section, "deep fake video" means a video, created with the intent to deceive, that appears to depict a real person performing an action that did not occur in reality
- ↑ https://capitol.texas.gov/BillLookup/History.aspx?LegSess=86R&Bill=SB751
- ↑ "New state laws go into effect July 1".
- ↑ 38.0 38.1 "§ 18.2-386.2. Unlawful dissemination or sale of images of another; penalty". w:Virginia. Retrieved 2021-01-23.
- ↑ "NVIDIA Open-Sources Hyper-Realistic Face Generator StyleGAN". Medium.com. 2019-02-09. Retrieved 2020-07-13.
- ↑
Harwell, Drew (2018-12-30). "Fake-porn videos are being weaponized to harass and humiliate women: 'Everybody is a potential target'". w:The Washington Post. Retrieved 2020-07-13.
In September [of 2018], Google added “involuntary synthetic pornographic imagery” to its ban list
- ↑ Kuo, Lily (2018-11-09). "World's first AI news anchor unveiled in China". Retrieved 2020-07-13.
- ↑ Hamilton, Isobel Asher (2018-11-09). "China created what it claims is the first AI news anchor — watch it in action here". Retrieved 2020-07-13.
- ↑ Suwajanakorn, Supasorn; Seitz, Steven; Kemelmacher-Shlizerman, Ira (2017), Synthesizing Obama: Learning Lip Sync from Audio, University of Washington, retrieved 2020-07-13
- ↑ Giardina, Carolyn (2015-03-25). "'Furious 7' and How Peter Jackson's Weta Created Digital Paul Walker". The Hollywood Reporter. Retrieved 2020-07-13.
- ↑ ReForm - Hollywood's Creating Digital Clones (youtube). The Creators Project. 2020-07-13.
- ↑ Debevec, Paul. "Digital Ira SIGGRAPH 2013 Real-Time Live". Retrieved 2017-07-13.
- ↑ In this TED talk video at 00:04:59 you can see two clips, one with the real Emily shot with a real camera and one with a digital look-alike of Emily, shot with a simulation of a camera - Which is which is difficult to tell. Bruce Lawmen was scanned using USC light stage 6 in still position and also recorded running there on a w:treadmill. Many, many digital look-alikes of Bruce are seen running fluently and natural looking at the ending sequence of the TED talk video.
- ↑ Pighin, Frédéric. "Siggraph 2005 Digital Face Cloning Course Notes" (PDF). Retrieved 2020-06-26.
- ↑ https://ict.usc.edu/about/
- ↑ "Images de synthèse : palme de la longévité pour l'ombrage de Gouraud".
- ↑ Mechanismus der menschlichen Sprache nebst der Beschreibung seiner sprechenden Maschine ("Mechanism of the human speech with description of its speaking machine", J. B. Degen, Wien).
- ↑ History and Development of Speech Synthesis, Helsinki University of Technology, Retrieved on November 4, 2006
How to protect yourself and others from covert modeling (transcluded)
Transcluded from How to protect yourself and others from covert modeling
Here are some basic tips on how to protect yourself and our societies from crimes committed by covert modeling of appearance and voice and synthesis from the models.


“I feel pretty confident that mister photograph man will not be selling much of my data to the no camera scene.”

“If your whole industry's shared secret is that digital look-alikes are going to pass human testing (i.e. people in the delusion that they are seeing images of humans) then popular culture product such as w:The Matrix will appear. It is widely known that meetings of surfaces, especially soft ones are very very difficult to do convincingly. Look-alikes of eyes meeting look-alikes of eye-lids are additionally hard to do, because there is also a liquid phase in the equation.”
“Sunglasses or sun glasses (informally called shades) are a form of w:protective eyewear designed primarily to prevent bright w:sunlight and w:high-energy visible light from damaging or discomforting the eyes.”

Protect your appearance from covert modeling
- Avoid uploading facial and full body photos and video of yourself to services where they are exposed to the whole Internet.
- If you need to upload photos, wear protective clothing, e.g. niqāb or burqa or protective accessories e.g. sunglasses.
- Consider getting a non-photorealistic w:avatar of your liking and use pictures of it to shield your appearance.
- Do not agree or get fooled to having your reflectance captured in a light stage.
Protect your voice from covert modeling
- Avoid uploading unaltered recordings of your w:human voice to services where they are exposed to the whole Internet.
- Consider altering the voice of your recordings if you must upload to the Internet with a voice changer or synthetic voice that does not match any human's voice.
- Avoid getting recorded by parties whose identity and reliability you cannot verify, especially if they do not expressly state how, where and for what purpose they will use the recording
- Ask for a voice changer to be applied if getting recorded to something that will be publicly broadcast
Protect your mind from the products of covert modeling
- Teach your loved ones the 2 key media literacy skills for this age of industrial disinformation:
- Not everything that looks like a video of people is actually a video of people
- Not everything that sounds like a recording of a known human's voice is actually a recording of that person's voice.
- Don't watch porn. A dodgy porn site or few is a hefty risk of seeing some digital look-alikes.
- Be critical of gossip about stuff claimed seen on the Internet.
Protect others from the products of covert modeling
- Read #Protect your mind from the products of covert modeling first. It is usually found above this. Also reading it to others has potential to help them.
- If you have strong evidence to suggest that some person may be under the influence of digital look-alikes, try to talk to them. The BCM! wiki glossary helps talk about things with their real names.
How to protect the humankind from products of covert appearance modeling
Adequate Porn Watcher AI (concept) is name for concept development to make an AI to look at and model all findable porn to provide protection the humankind and individual humans by modeling what it sees.
The reason why APW_AI makes sense is that if you can trust the service providers to keep safe your own model it will alert you when it finds something that looks really like a match and therefore lifting the looming threat of digital look-alike attacks and the destructiveness of the attacks that take place considerably lower and thus also the monetary value to the criminals.
How to protect our societies from covert modeling
Contact your representatives
Contact your representatives and ask them ...
- If they are aware of these new classes of disinformation weapons?
- What is their position on the criminalizing covert modeling-question?
- If steps are being taken to protect the judiciary from covert modeling?
- What, if anything, they are doing to put this hyper-modern lawlessness under some check?
- To talk with colleagues and also publicly about the problems caused by covert modeling.
If they don't believe ask them to...
- Work for the creation of fact-finding taskforce to ascertain the truth that synthetic terror porn has been used as a weapon for a longer time.
How to protect judiciaries from covert modeling
Digital look-alikes and digital sound-alikes technologies prompt some changes to w:rules of evidence and updates to what should be deemed deniable.
Recordings that sound like someone saying something may not be genuine and therefore the suspect should be allowed to state to the court "I did never say that thing you got on tape."
Pictures and videos that looks like someone doing something may not be genuine and therefore the suspect should be allowed to state to the court "I am not in that image/video."
If media forensics proves beyond suspicion the genuinity of the media in question or if credible witness to its creation is found, the media should be considered evidence.
Help against appearance and voice theft
See Help against appearance and voice theft.
References